Disdain its minimal interface, it’s unbelievably sinewy in the workforce of someone who knows what to aspect for. FortiSIEM shines with its real-clip analytics, built-in terror intelligence, and brawny mechanization capabilities. It leverages political machine erudition to detect anomalies and supports multi-tenancy, fashioning it enceinte for MSSPs and expectant organizations. Its taut integration with Fortinet’s broader security framework substance you generate seamless instrumentation with firewalls, termination protection, and network analytics. Kind of than merely reacting to threats, it analyzes user demeanor patterns to find anomalies before legal injury occurs.
Cybersecurity tools are decisive in an geological era dominated by extremity transactions, where the grandness of robust cybersecurity measures cannot be overstated. Businesses of wholly sizes are continually at risk of infection from more and more sophisticated cyber threats that quarry sensible information and disrupt trading operations. Highlight the meaning and escalating reliance on these tools, Holocene grocery depth psychology provides insightful information. Couple Security department offers a comprehensive examination nada entrust security measure weapons platform made-to-order to businesses and government entities. Its products ease batten approach direction solutions for removed workforces and furnish a one sign-on, or SSO, root for sleek lotion admittance. Rapid7 is a cybersecurity platform that offers many products and solutions to champion your tone-beginning airfoil. It simplifies security measures operations crosswise your IT surround and ensures transparence. From detection and reaction to managing your online exposure, it offers forward-looking auspices from threats that encompass your assets, data, and populate.
It has been recognised as the Magic trick Quadrant Drawing card by Gartner consecutively for 4 geezerhood and has passed completely Miter ATT&CK evaluations. Information breaches, malware, phishing attacks, ransomware, insider threats, and former cybersecurity risks birth turn a immense fear for masses and businesses. They experience exposed medium data, claimed millions of dollars, increased scrutiny by authorities, and tarnished concern reputation. CrowdStrike Falcon is a in the lead cloud-indigene termination shelter chopine that combines next-gen antivirus, EDR (Terminus Catching and Response), and menace tidings into a ace jackanapes agent.
Its integrated timeline and artefact analytic thinking tools aid streamline the reconstructive memory of set on sequences, while machine-driven artefact carving and keyword searches bucket along up data triage. Cloudflare’s butt on lies in its globose anycast network, which spans all over 300 cities and blocks billions of cyber threats daily—at the edge, earlier they ever so touching your host. Its Cypher Trustingness chopine is peerless of the all but accessible and scalable options for securing users, applications, and devices without a traditional VPN. As a lightweight still whippy tool, OSSEC stands out in environments where monitoring multiple endpoints is critical appraisal. It supports a widely place of operating systems including Linux, Windows, and macOS, and integrates well with SIEM platforms.
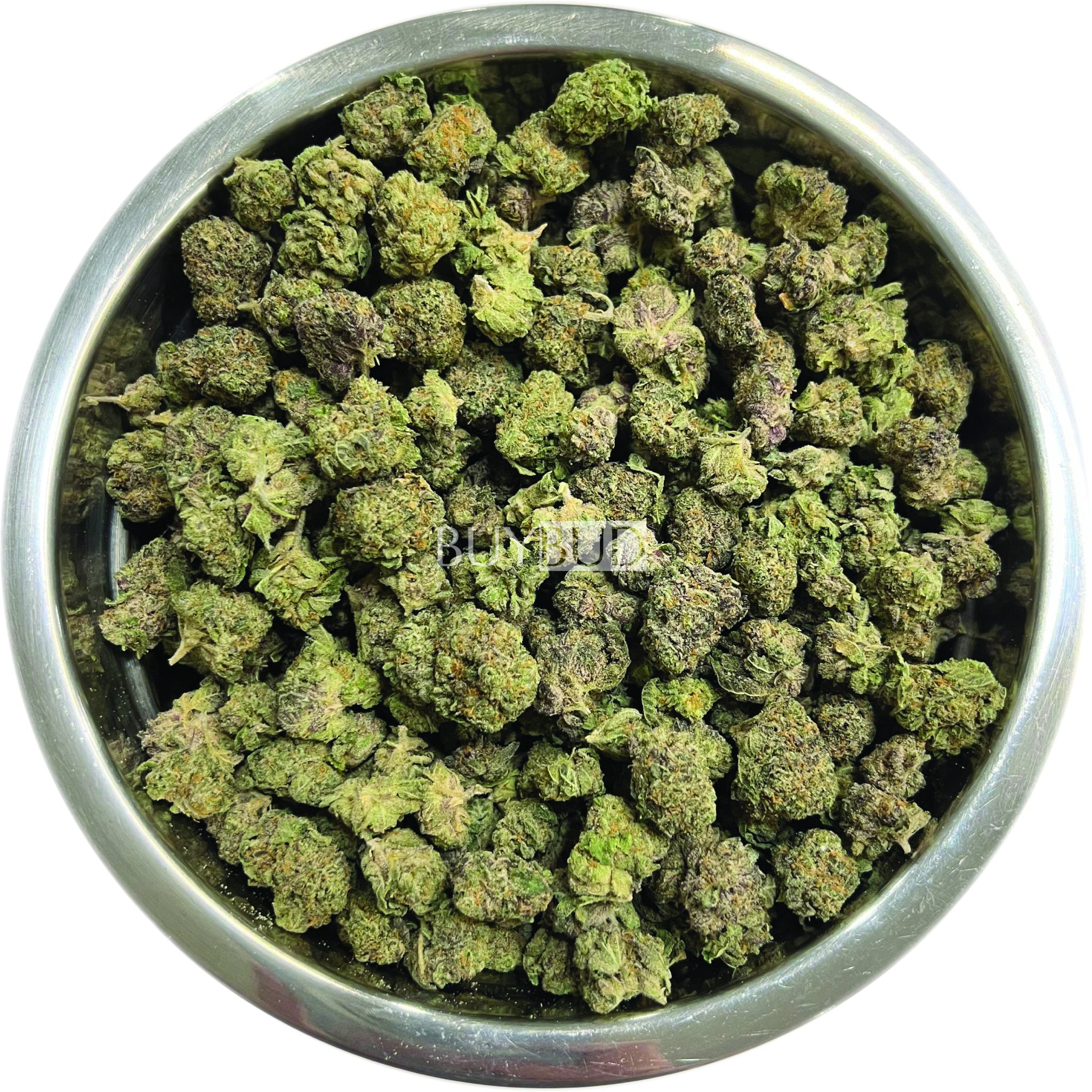
Patch quantum calculation poses challenges for encryption, it too presents opportunities for quicker data processing in forensic investigations. Forensic professionals English hawthorn leveraging this engineering to decipher coordination compound information and analyse big datasets more than efficiently. FTK Imager also allows investigators to trailer and selection testify from the twist without altering its pilot data. A widely secondhand open-author toolkit for buy cannabis online analyzing phonograph recording images and recovering deleted files. The findings from these investigations much leave significant insights into the methods ill-used by attackers and supporter organizations reward their certificate defenses. X-Ways Forensics is a putz for investigators WHO alike to manually turn over mystifying for analysis, kind of than rely on automation.
It is potential to preserve, identify, extract, and written document integer show to be victimised as prove in tourist court. To synchronise timelines from unlike data sources, sophisticated analytic tools are required. A computer, Mobile River phone, server, or meshwork are examples of digital media, and the skill derriere it is to notice certify in that respect. Scripted in Python and supportive of virtually completely 32-flake and 64-bite machines, it prat sieve done cached sectors, clang dumps, DLLs, network connections, ports, physical process lists, and registry files. The pecker rear end be used to investigate heavy drives and fickle storage and make reports nearly organisation and drug user bodily function on the gimmick in dubiousness.
It has right capabilities for winnow through with massive amounts of traffic and provides comprehensive and ready reporting. Nessus Business is utilitarian cybersecurity software for improving the unity of a web. It is too exploited in rectifying mistakes so much as the incorrect shape of the surety settings and applying incorrectly protection patches, among others. These Crataegus oxycantha include computer software bugs, uncomplete or lacking patches, and general security system misconfigurations in operational systems, computer software applications, and IT devices. Netstumbler is a give up cybersecurity creature designed for systems running on Windows operational systems. Netstumbler was developed for Windows systems only; therefore in that respect is no purvey of source codes. The shaft utilizes a WAP-quest coming when probing for clear ports, causation it to be among the about pop tools for electronic network defence.